MailMapr
Email Viewer, Phishing Detection & Forensic Analysis for macOS
Open. Analyze. Investigate. Report.
Requires macOS 14.0 Sonoma or later
Email Viewer, Phishing Detection & Forensic Analysis for macOS
Open. Analyze. Investigate. Report.
Requires macOS 14.0 Sonoma or later
Whether you're investigating phishing, auditing communications, or simply need to open email files
Investigate phishing attacks, detect spoofing, identify IoCs and compromised accounts.
Review email evidence with chain-of-custody. Export forensic reports for legal proceedings.
Open and view EML/MSG files. Convert between formats. Analyze suspicious emails from users.
No Outlook or email client needed — open any email file directly
Open EML, EMLX, MSG (Outlook), and MBOX archives without any email client installed. View full message body, headers, attachments, and metadata.
Quick View mode — open and inspect email files without creating a project.
Export email evidence to PDF for sharing with teams, legal departments, or management. Generate professional forensic reports in HTML and PDF formats.
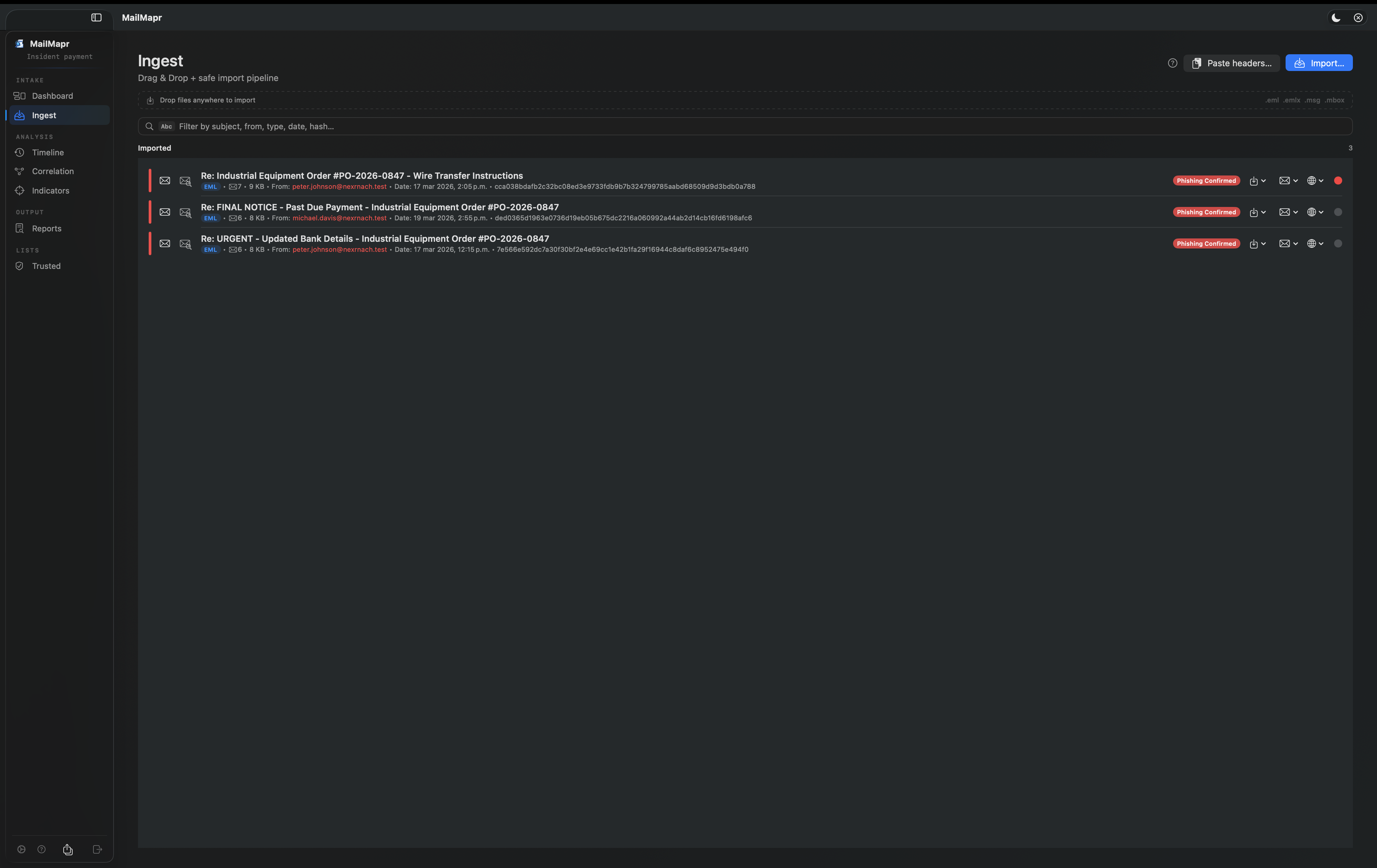
Batch analysis — import multiple files at once via drag & drop.
Everything you need to investigate email-based threats
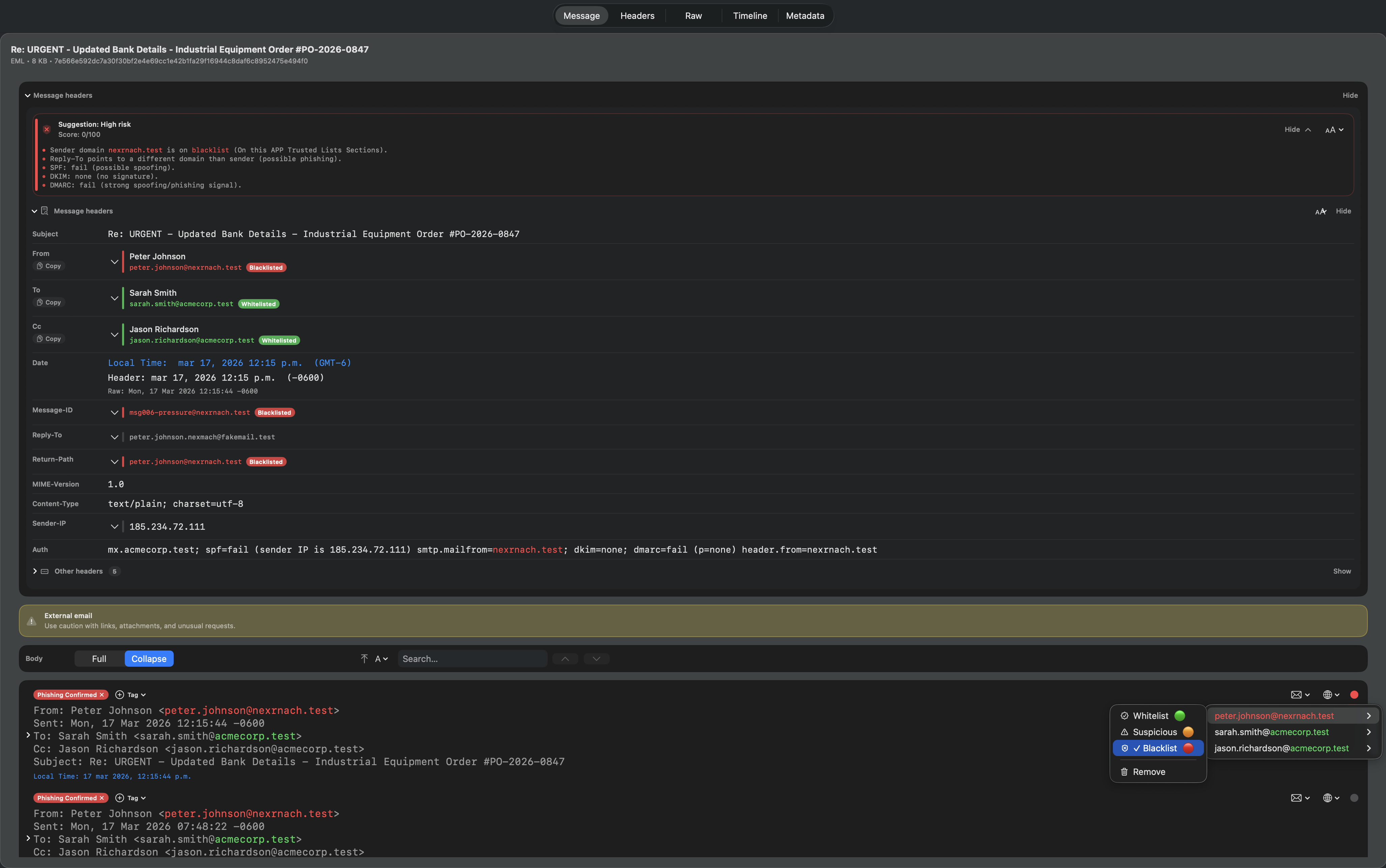
Automatic risk scoring (0–100) per email. Detect header spoofing, domain mismatches, authentication failures (SPF, DKIM, DMARC), and suspicious patterns.
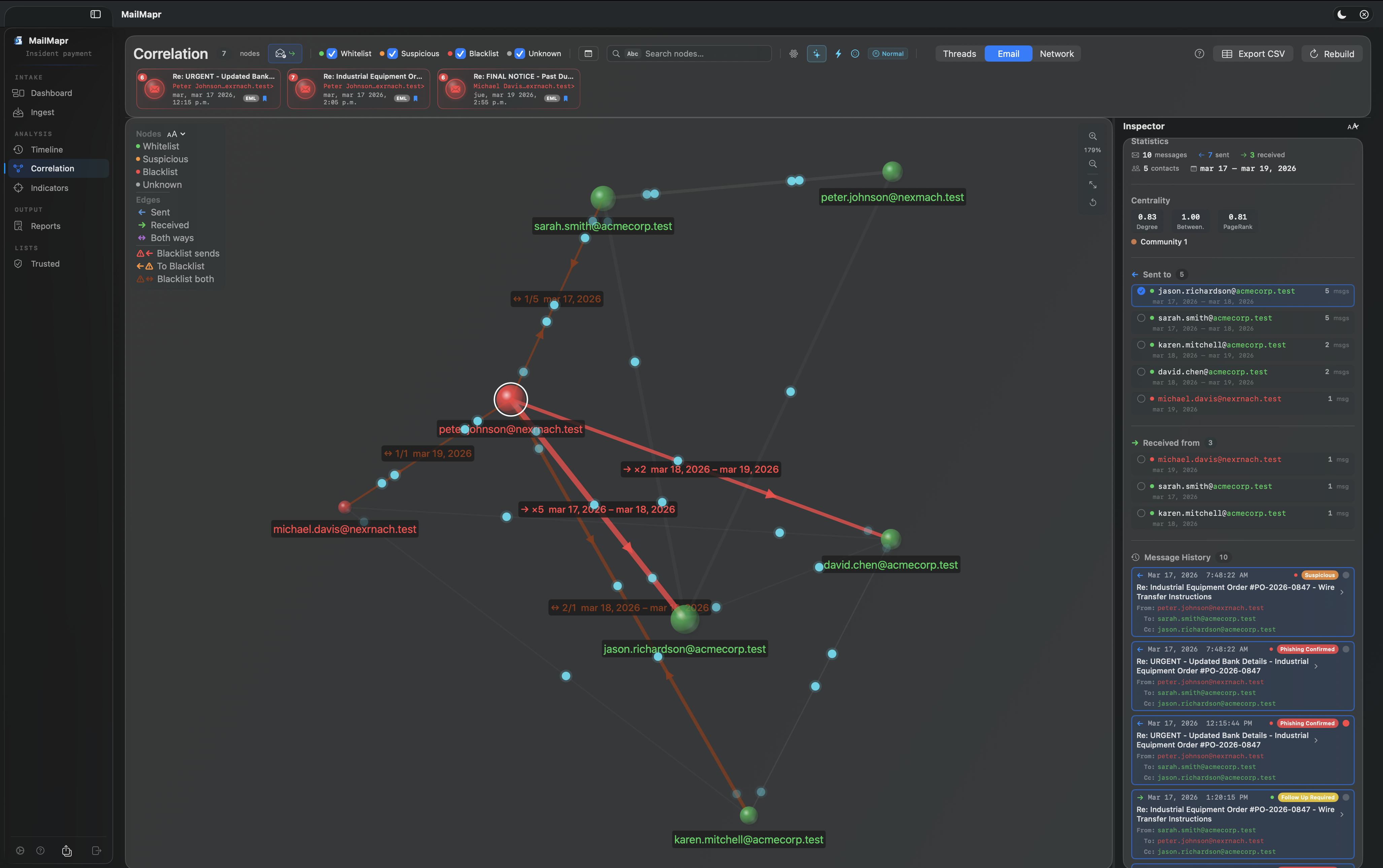
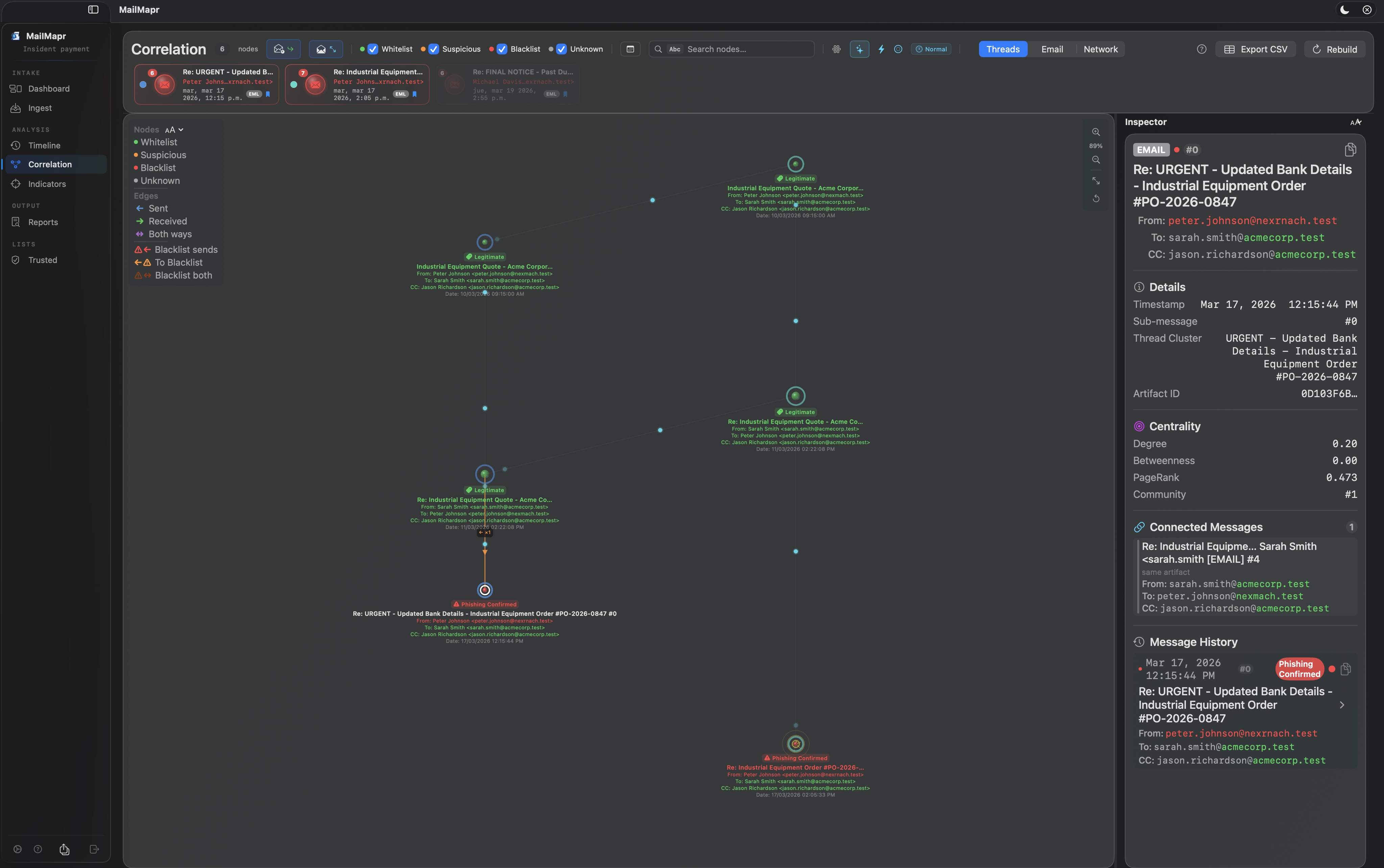
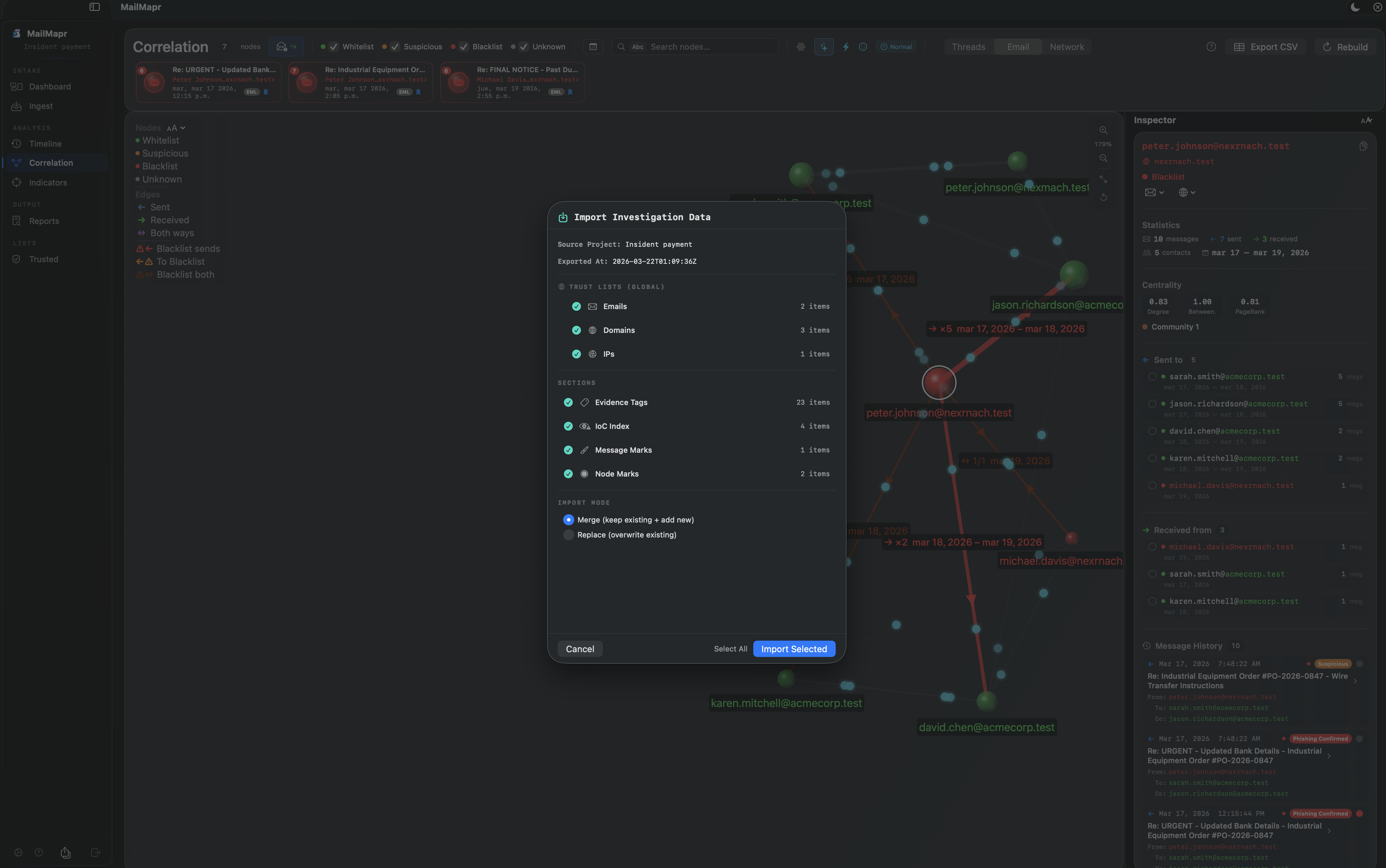
Emails, domains, and IPs color-coded by trust: green (whitelist), orange (suspicious), red (blacklist). Instant visual threat assessment.
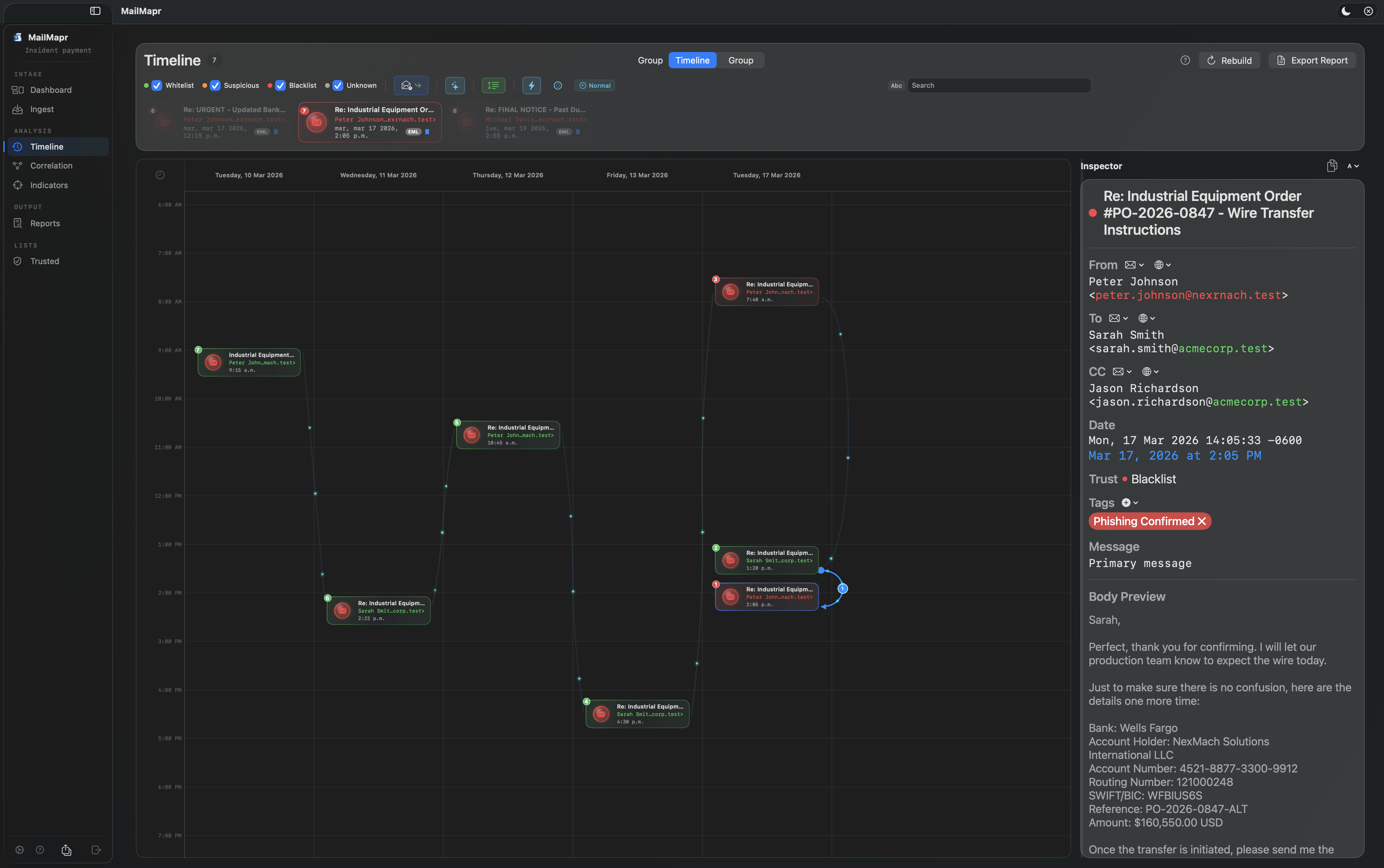
Visualize email communication patterns over time. Identify anomalies, timeline gaps, and correlate events across an incident.
Map communication relationships between all addresses. Detect communities, identify attack hubs and entry vectors visually.
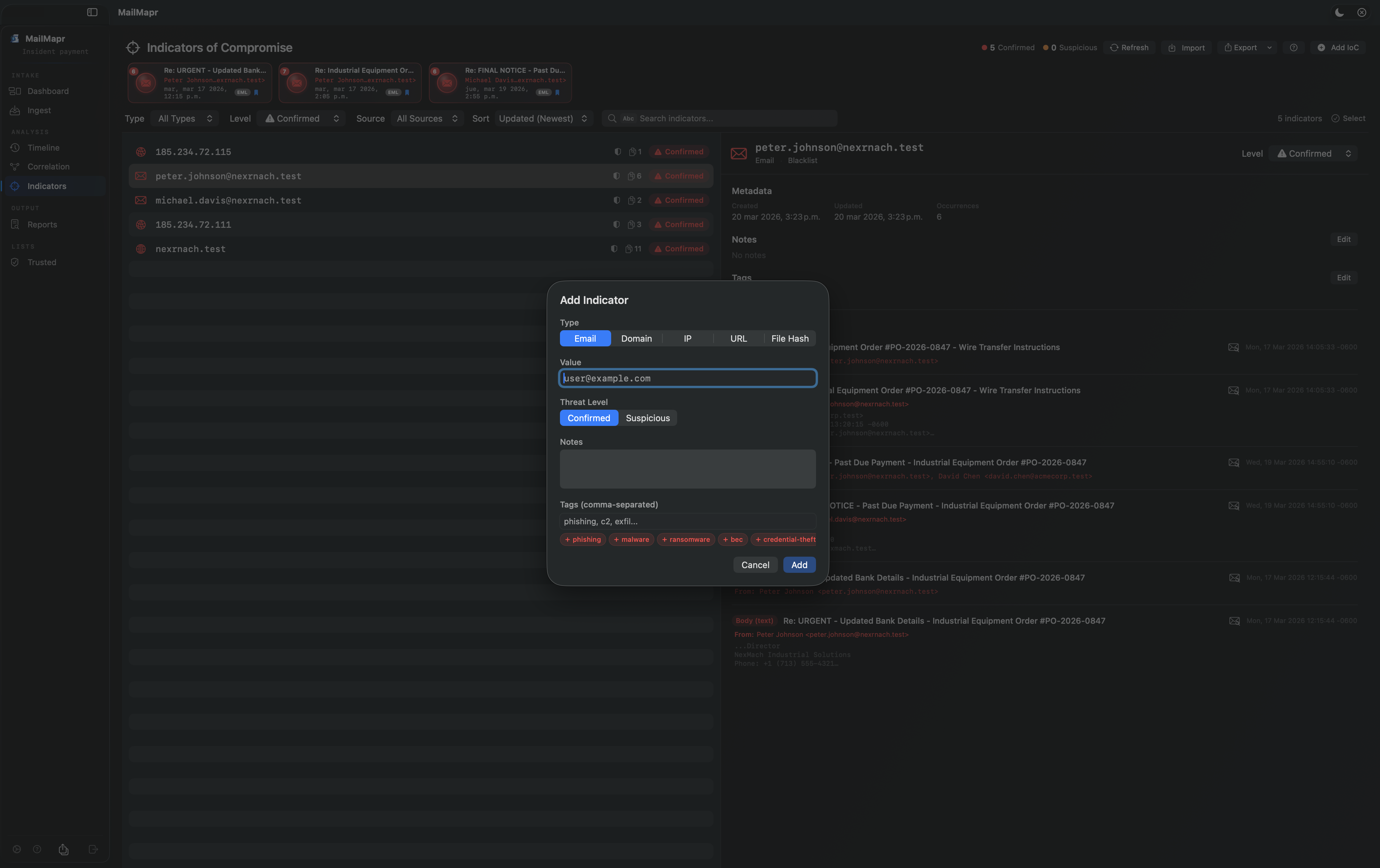
Track malicious emails, domains, and IPs as IoCs. Record threat level, source, and occurrences. Export for threat intelligence sharing.
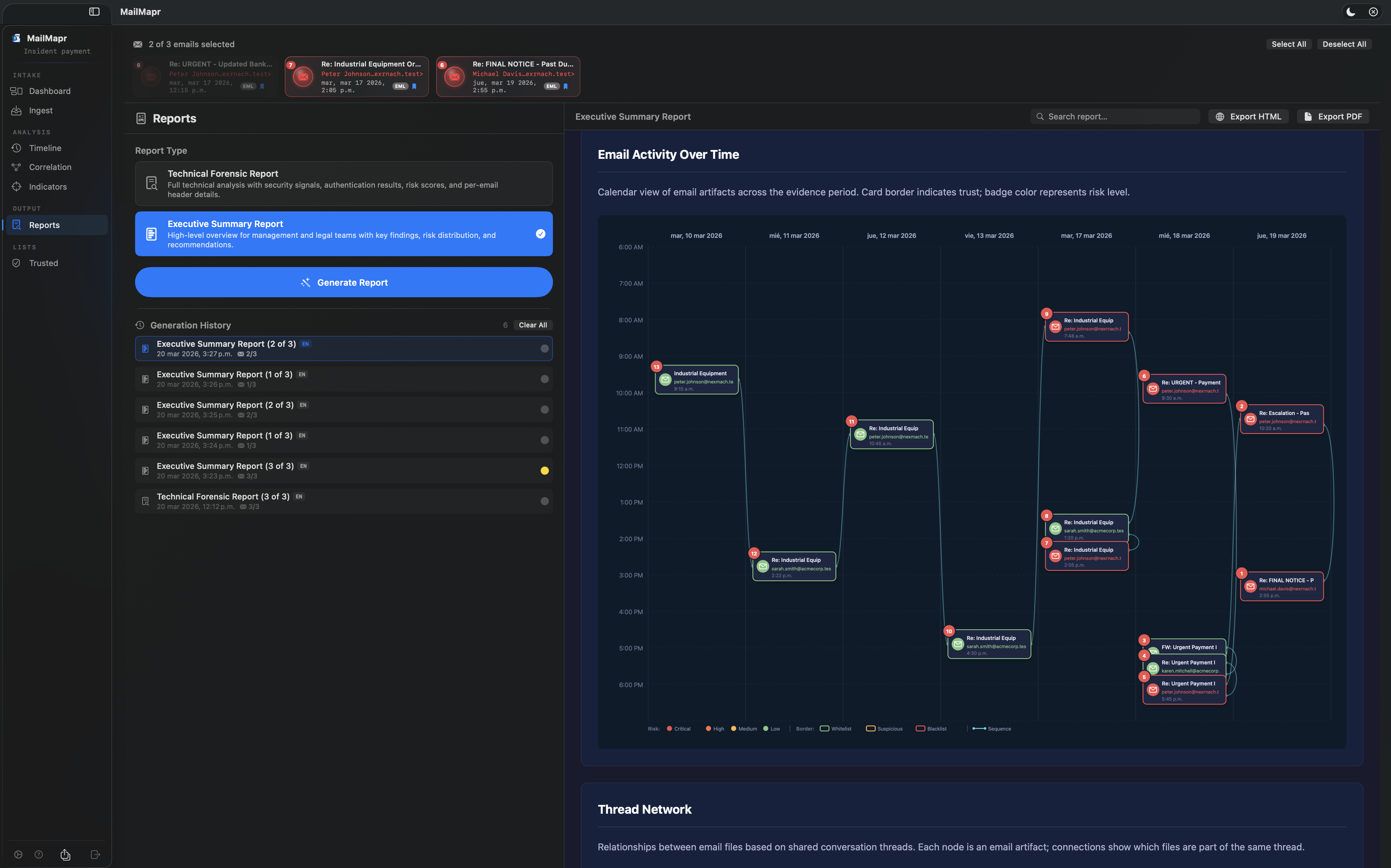
Generate Technical Forensic and Executive Summary reports. Full email analysis, risk breakdown, trust distribution, and per-incident details.
Identify recurring contacts across multiple investigations. Detect coordinated attacks spanning different cases and timeframes.
100% offline analysis. No data leaves your Mac. No cloud, no accounts, no tracking. App Sandbox protected. Your evidence stays yours.
Watch MailMapr in action
Click any screenshot to enlarge
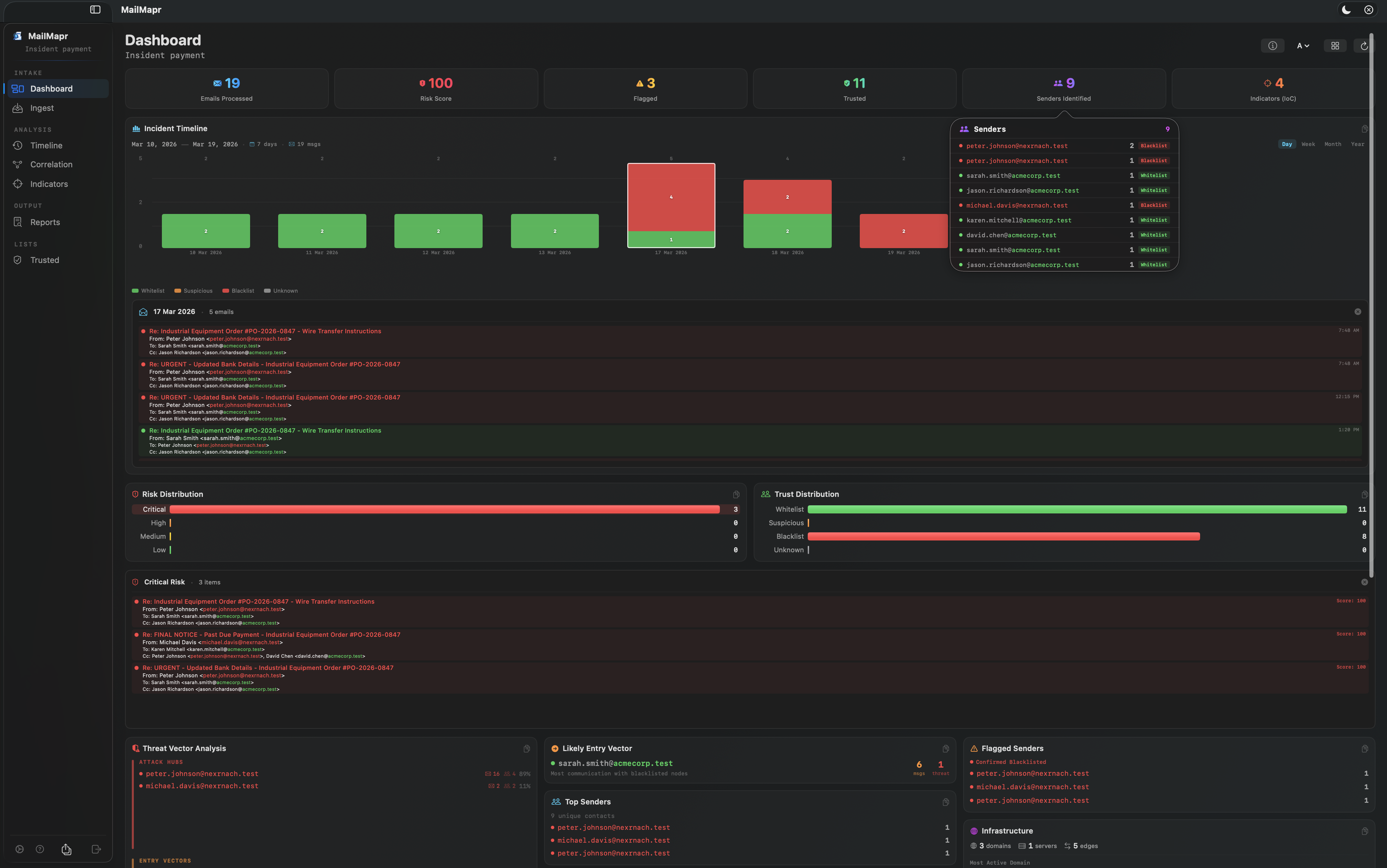
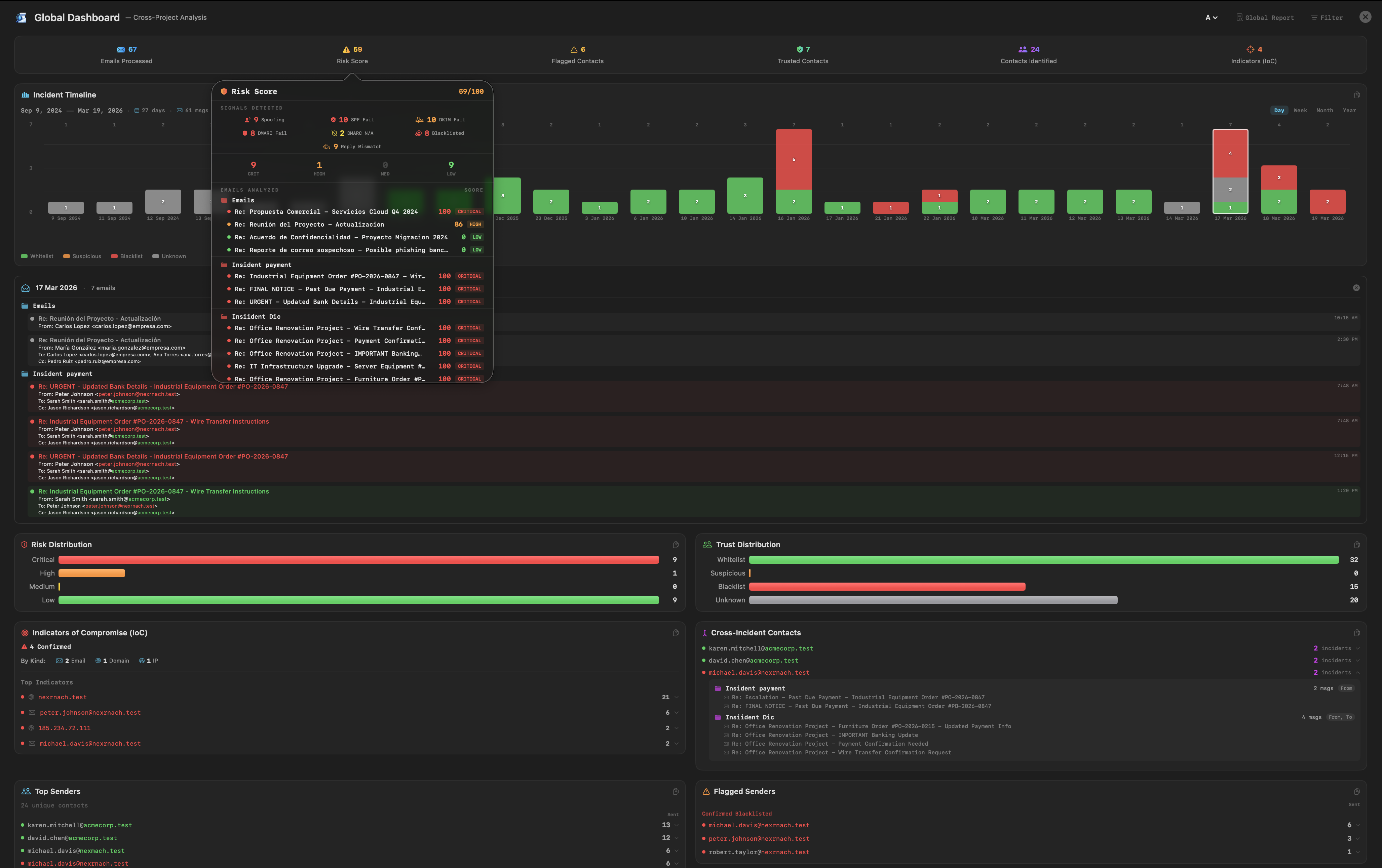
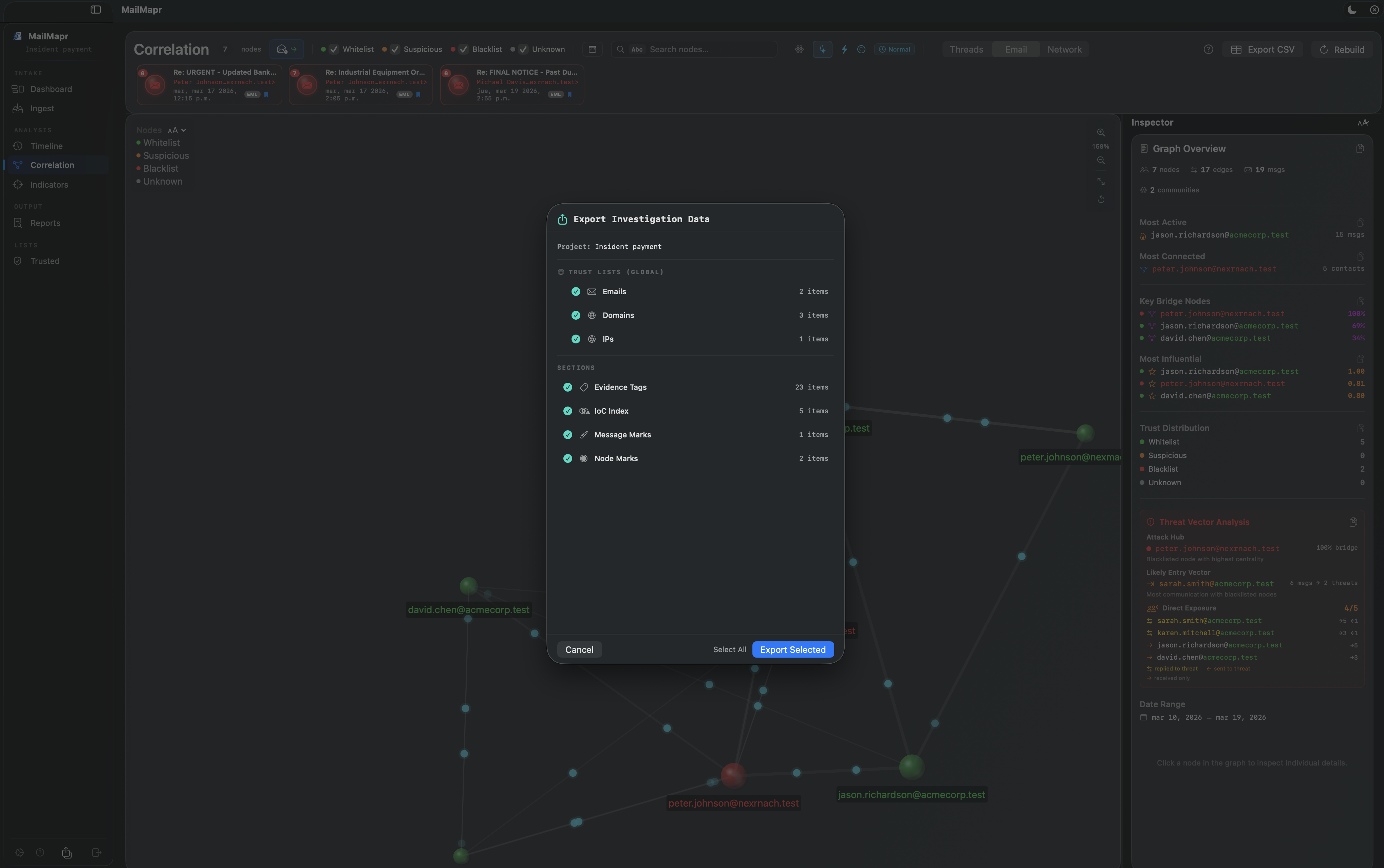

All email addresses, company names, and domains shown in screenshots are entirely fictitious and created for demonstration purposes using the IANA-reserved .test TLD.
From email import to forensic report in four steps
Organize your investigation by creating a project. Each project keeps evidence, analysis, and reports separate and self-contained.
Drag and drop EML, MSG, or MBOX files into the Ingest module. MailMapr parses headers, body, attachments, and metadata automatically. Use Quick View to inspect files without a project.
Review phishing risk scores, SPF/DKIM/DMARC results, and trust color coding. Use Timeline, Correlation graphs, and Indicators to map the full attack picture.
Export Technical Forensic or Executive Summary reports as HTML or PDF. Share findings with management, legal teams, or incident responders.